AdGuard Home & DNS over TLS issue
Since last night, I have issue with all of of my AdGuard Home server with DNS over TLS enabled (port 853). All client unable to connect it using DNS over TLS although it work flawlessly since last year.
I also tried @Freek sg.adhole.org DNS over TLS project which is use similar configuration. The issue still persist.
All of my client can use dns.google and 1dot1dot1dot1.cloudflare-dns.com without any issue.
This is the log from Stubby, DNS over TLS client for Windows 10, when using @Freek sg.adhole.org. The log from my AdGuard Home also similar with this.
[20:07:18.737563] STUBBY: Stubby version: Stubby 0.3.0
[20:07:18.779579] STUBBY: Read config from file C:\Program Files\Stubby\stubby.yml
[20:07:18.781562] STUBBY: DNSSEC Validation is OFF
[20:07:18.781562] STUBBY: Transport list is:
[20:07:18.781562] STUBBY: - TLS
[20:07:18.782565] STUBBY: Privacy Usage Profile is Strict (Authentication required)
[20:07:18.782565] STUBBY: (NOTE a Strict Profile only applies when TLS is the ONLY transport!!)
[20:07:18.782565] STUBBY: Starting DAEMON....
[20:07:20.060514] STUBBY: --- SETUP(TLS): : Adding Windows certificates from system root store to CA store
[20:07:20.072514] STUBBY: --- SETUP(TLS): : Completed adding Windows certificates to CA store successfully
[20:07:20.073492] STUBBY: 210.16.120.48 : Conn opened: TLS - Strict Profile
[20:07:20.186965] STUBBY: 210.16.120.48 : Verify failed : TLS - *Failure* - (10) "certificate has expired"
[20:07:20.187843] STUBBY: 210.16.120.48 : Conn closed: TLS - *Failure*
[20:07:20.187843] STUBBY: *FAILURE* no valid transports or upstreams available!
[20:07:20.187843] STUBBY: 210.16.120.48 : Conn closed: TLS - *Failure*
[20:07:20.188839] STUBBY: *FAILURE* no valid transports or upstreams available!
[20:07:20.188839] STUBBY: 210.16.120.48 : Conn closed: TLS - Resps= 0, Timeouts = 0, Curr_auth = Failed, Keepalive(ms)= 0
[20:07:20.188839] STUBBY: 210.16.120.48 : Upstream : TLS - Resps= 0, Timeouts = 0, Best_auth = Failed
[20:07:20.189840] STUBBY: 210.16.120.48 : Upstream : TLS - Conns= 0, Conn_fails= 1, Conn_shuts= 0, Backoffs = 0
[20:07:23.943510] STUBBY: *FAILURE* no valid transports or upstreams available!
Could not schedule query: None of the configured upstreams could be used to send queries on the specified transports
[20:07:29.922561] STUBBY: *FAILURE* no valid transports or upstreams available!
Could not schedule query: None of the configured upstreams could be used to send queries on the specified transports
[20:07:33.940687] STUBBY: *FAILURE* no valid transports or upstreams available!
Could not schedule query: None of the configured upstreams could be used to send queries on the specified transports
I am not sure this is LetsEncrypt SSL issue or AdGuard Home issue. Do you also have any issue with your AdGuard Home & DNS over TLS configuration?
⭕ A simple uptime dashboard using UptimeRobot API https://upy.duo.ovh
⭕ Currently using VPS from BuyVM, GreenCloudVPS, Gullo's, Hetzner, HostHatch, InceptionHosting, LetBox, MaxKVM, MrVM, VirMach.



Comments
I was going to tag Freek but you already have - I'm sure he can help.
Thank you @Mr_Tom, did you perhaps face this issue too?
⭕ A simple uptime dashboard using UptimeRobot API https://upy.duo.ovh
⭕ Currently using VPS from BuyVM, GreenCloudVPS, Gullo's, Hetzner, HostHatch, InceptionHosting, LetBox, MaxKVM, MrVM, VirMach.
Should be working?
Stubby
upstream_recursive_servers:
- address_data: 210.16.120.48
tls_auth_name: "sg.adhole.org"
Maybe due to LE's cross cert expiring?
I had the same issues.
Had to recreate the certs using:
A restart of AdGuard later, and it was working again.
FreeVPS.org - Grab a free VPS!
That is my thought too
What is your certbot version, I am running those command with certbot 0.31.0 but there is error
certbot: error: unrecognized arguments: --preferred-chain ISRG Root X1⭕ A simple uptime dashboard using UptimeRobot API https://upy.duo.ovh
⭕ Currently using VPS from BuyVM, GreenCloudVPS, Gullo's, Hetzner, HostHatch, InceptionHosting, LetBox, MaxKVM, MrVM, VirMach.
I'm using 'certbot 1.12.0'.
FreeVPS.org - Grab a free VPS!
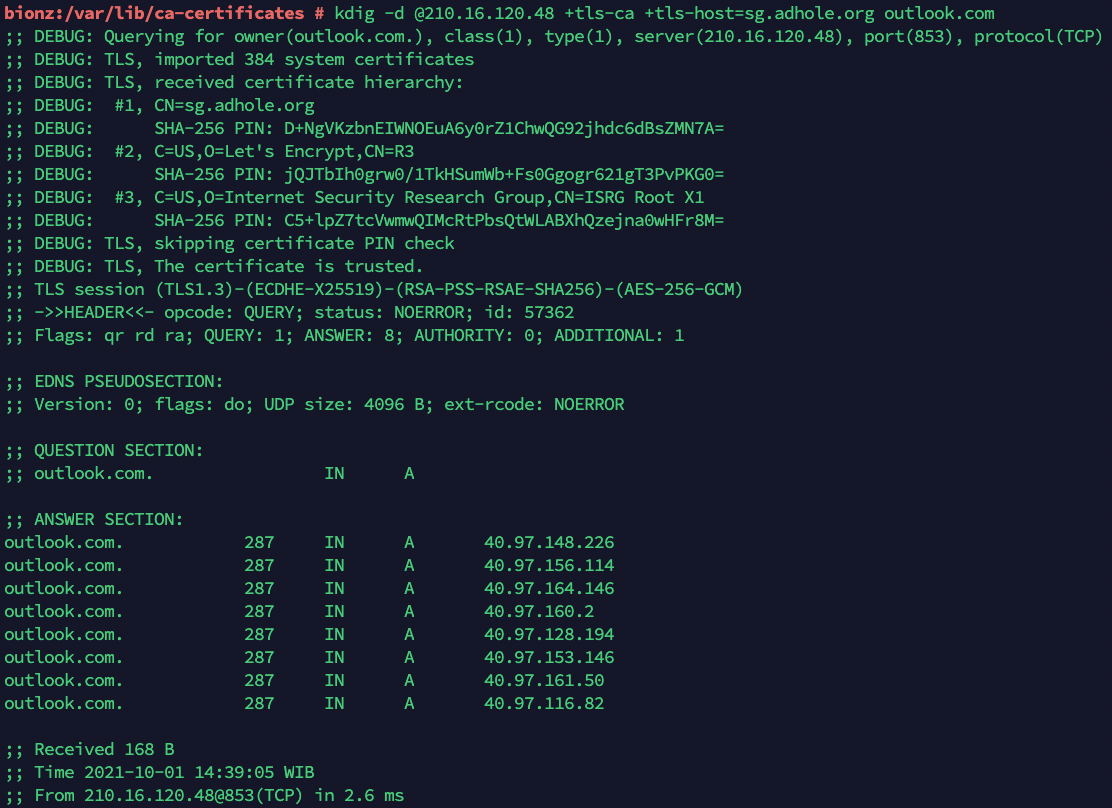
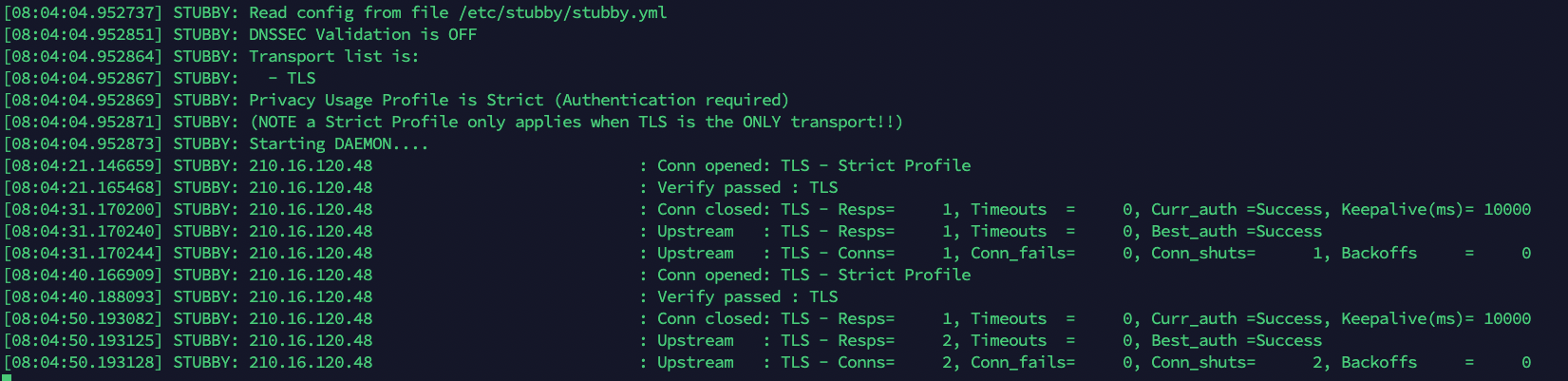
That is strange, this is my result of stubby using
sg.adhole.organd my owh AdGuard HomeThis is result of stubby using dns.google
⭕ A simple uptime dashboard using UptimeRobot API https://upy.duo.ovh
⭕ Currently using VPS from BuyVM, GreenCloudVPS, Gullo's, Hetzner, HostHatch, InceptionHosting, LetBox, MaxKVM, MrVM, VirMach.
I don't have a lot of time to go into details right now, but LetsEncrypt's old root certificate has expired yesterday (IdentTrust DST Root CA X3). Some websites are facing issues (source).
Probably your best bet is to look into the CA certificate your client is using to verify the TLS certificate.
for those using acme.sh:
--force --server letsencrypt --preferred-chain "X1"Action and Reaction in history
Thank you @daffy & @elliotc the new generated certificate working, Now.
⭕ A simple uptime dashboard using UptimeRobot API https://upy.duo.ovh
⭕ Currently using VPS from BuyVM, GreenCloudVPS, Gullo's, Hetzner, HostHatch, InceptionHosting, LetBox, MaxKVM, MrVM, VirMach.
Excellent!
Let's just say I was rather frustrated when my phone suddenly stopped working with it yesterday and didn't have time to check it until this morning.
FreeVPS.org - Grab a free VPS!